- H2 2022 was the period with the highest rate of attacks against industrial sectors with 34% of computers affected.
- Attacks carried out using malicious scripts, phishing pages (JS and HTML) and denylisted resources were also on the rise.
- Attacks on automotive manufacturing and energy sector showed unprecedented growth and accounted for 36.9 percent and 34.5 percent of all industries.
LONDON, 6th March 2023 - In H2 2022, Kaspersky security solutions blocked malware from 7,684 different families on industrial automation systems, such as building automation, automotive, oil and gas, energy and engineering. This number is slightly more (6%) compared with the previous half of the year and almost 1.5 times more than in the second half of 2021. Overall, the 2022 ended up being the year that accounts for the highest percentage of OT computers affected by malware (40.6%).
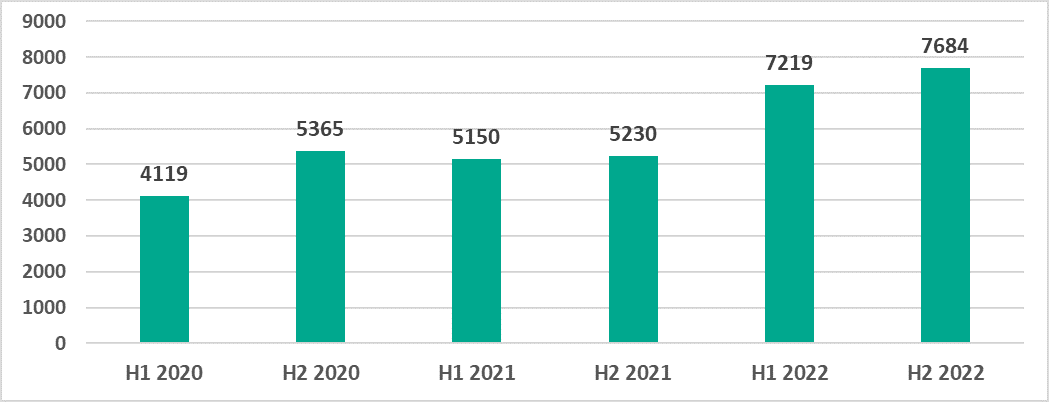 Number of
malware families blocked on ICS computers
Number of
malware families blocked on ICS computers
In terms of malware categories, only the two top rankings showed growth in the second half of 2022, namely – malicious scripts and phishing pages (JS and HTML), which are distributed both online and via email, anddenylisted internet resources, which are used to distribute malicious scripts and phishing pages.
In the UK, the percentage of malicious scripts blocked on ICS computers was 4.9%, followed by 3.4% of denylisted internet resources. Spyware, which is used for unauthorized remote access to deliver next-stage payloads such as ransomware, was the third most common attack, which was blocked on 1.7% of OT machines.
Threat actors use malicious scripts for a broad range of tasks – from collecting information, tracking activity, and redirecting browser requests to malicious web resources, to downloading various malicious programs or loading malware (spyware or tools for covert cryptocurrency mining) in the user’s browser.
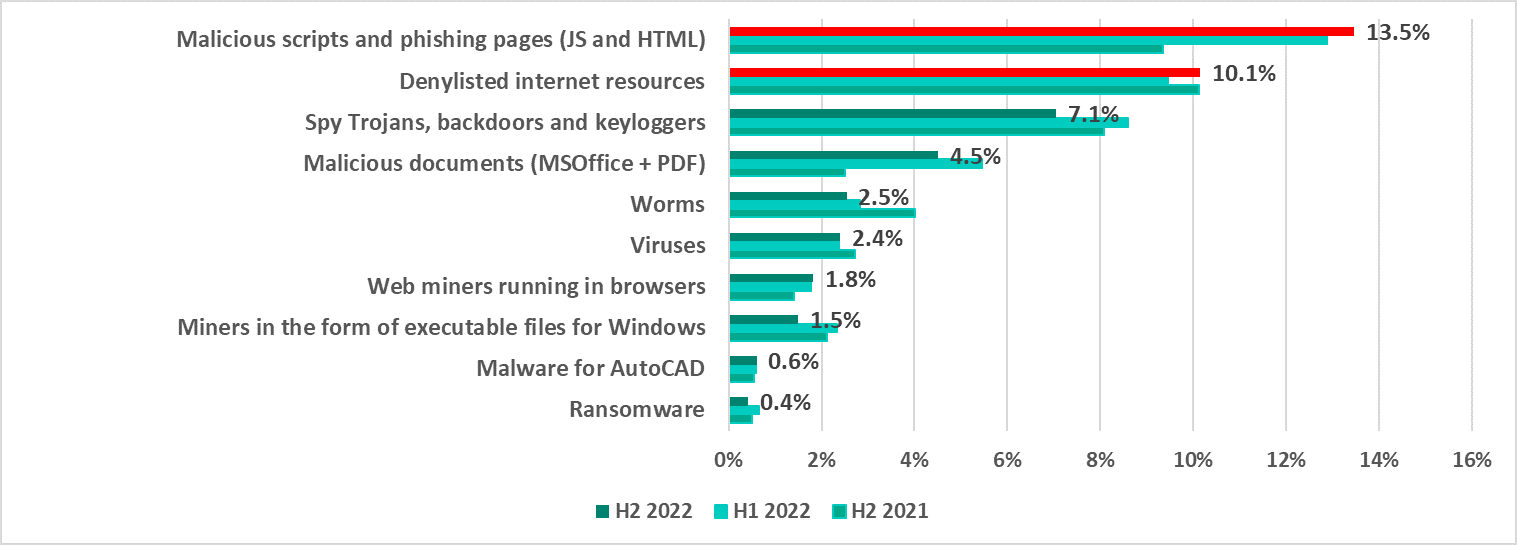 Percentage of ICS computers* in which the activity of malicious objects
from different categories was prevented
Percentage of ICS computers* in which the activity of malicious objects
from different categories was prevented
Unexpectedly, Northern Europe became the only region that showed a growth in ransomware attacks and malware spread via email clients. When observing other geographical regions, Middle East remain the region that is highly affected by ransomware attacks and being number 3 in the TOP regions ranked by percentage of ICS computers on which malicious email attachments and phishing links were blocked, while Africa, ME, Asia and LatAm top regional rankings with most OT computers compromised using removable devices.
The situation varied in different industries. As for H2 2022, the automotive industry (+4.6 p.p.) and energy sector (+1 p.p.) showed growth in terms of the OT computers that were affected. In other industries tracked, the percentage decreased.
“Overall, 2022 stands out for its abnormal absence of any seasonal changes. Our team observed a steadily high rate of attacks on industrial sectors – without a typical drop in attacks during summer vacations or winter holidays period. However, the growing attack rates in industrial sectors, that are being conducted using social engineering, seem alarming. We strongly recommend customers in these sectors to revise their existing approach to security and check whether all security systems are up-to-date and their personnel is well-trained,” comments Kirill Kruglov, senior researcher at Kaspersky ICS CERT.
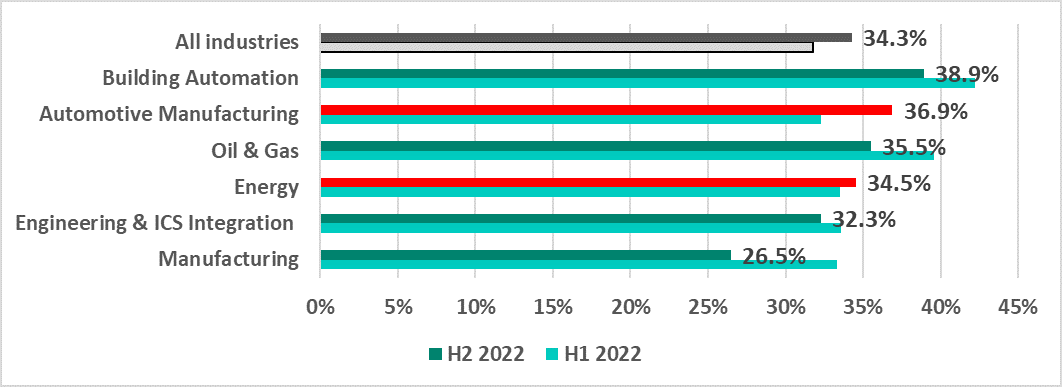 Percentage of ICS computers in which malicious objects were blocked in some
industries
Percentage of ICS computers in which malicious objects were blocked in some
industries
Read more about the ICS threat landscape in H2 2022 on the Kaspersky ICS CERT website.
To keep your OT computers protected from various threats, Kaspersky experts recommend:
- Conducting regular security assessments of OT systems to identify and eliminate possible cyber security issues.
- Establishing continuous vulnerability assessment and triage as a basement for effective vulnerability management process. Dedicated solutions like Kaspersky Industrial CyberSecurity may become an efficient assistant and a source of unique actionable information, not fully available in public.
- Performing timely updates for the key components of the enterprise’s OT network; applying security fixes and patches or implementing compensating measures as soon as it is technically possible is crucial for preventing a major incident that might cost millions due to the interruption of the production process.
- Using EDR solutions such as Kaspersky Endpoint Detection and Response for timely detection of sophisticated threats, investigation, and effective remediation of incidents.
- Improving the response to new and advanced malicious techniques by building and strengthening your teams’ incident prevention, detection, and response skills. Dedicated OT security trainings for IT security teams and OT personnel is one of the key measures helping to achieve this.
Industrial sector under threat: 40% of operational technology (OT) computers were affected by malware in 2022
Kaspersky
Related Articles Press Releases
Digital resolutions as important as health kicks in 2024
Almost half of people now make digital resolutions for 2024. These include stronger passwords and gadget detoxes as part of daily routines.Read More >Kaspersky Research Reveals C-Suite’s Plan to Plug Skills Gap with Gen AI
Although most remain “unsure how it actually works”, 40% of C-level executives are planning to use AI and the advantages that can be gained through Generative AI (Gen AI) such as ChatGPT to cover critical skills shortages, according to new research by Kaspersky. As expected, the survey of almost 2,000 C-level execs across Europe reveals Gen AI to be firmly on the business agenda with almost all (95%) respondents regularly discussing ways to maximise value from the technology at the most senior level, despite 91% expressing a need to develop a deeper understanding of how it works and where the data goes once inputted.Read More >Date or DAIte? Kaspersky Study Reveals Over Half of Single Men Would Use ChatGPT to “Deceive” Potential Dates
- 75% of single people surveyed would use ChatGPT to improve their chat up lines - Over half (52%) of women would use ChatGPT to increase the amount of people they are talking to at one time on dating apps - Dating expert laments “deceiving” use of chatbots “a real reason for concern”Read More >