No sooner was Cyberpunk 2077 released for Windows and consoles than we came across a “beta version for Android” online. It was completely free to download from a site bearing the name cyberpunk2077mobile[.]com. The game’s actual developer has yet to announce any mobile version of the game, so we decided to investigate.
Cyberpunk 2077 for Android? No, it’s ransomware
The website for the alleged mobile version looks nothing like Cyberpunk 2077‘s official site — it looks more like Google Play, in fact. Its creators claim the beta version was released on the same day as the official release, and (at the time of this post) had been downloaded about 1,000 times. Some users had even left feedback, saying it wasn’t bad for a beta version.
Although the website lists the app’s size at 3.4GB, the file is less than 3MB. Did the developers also create some kind of futuristic compression technology on the side? Not likely.
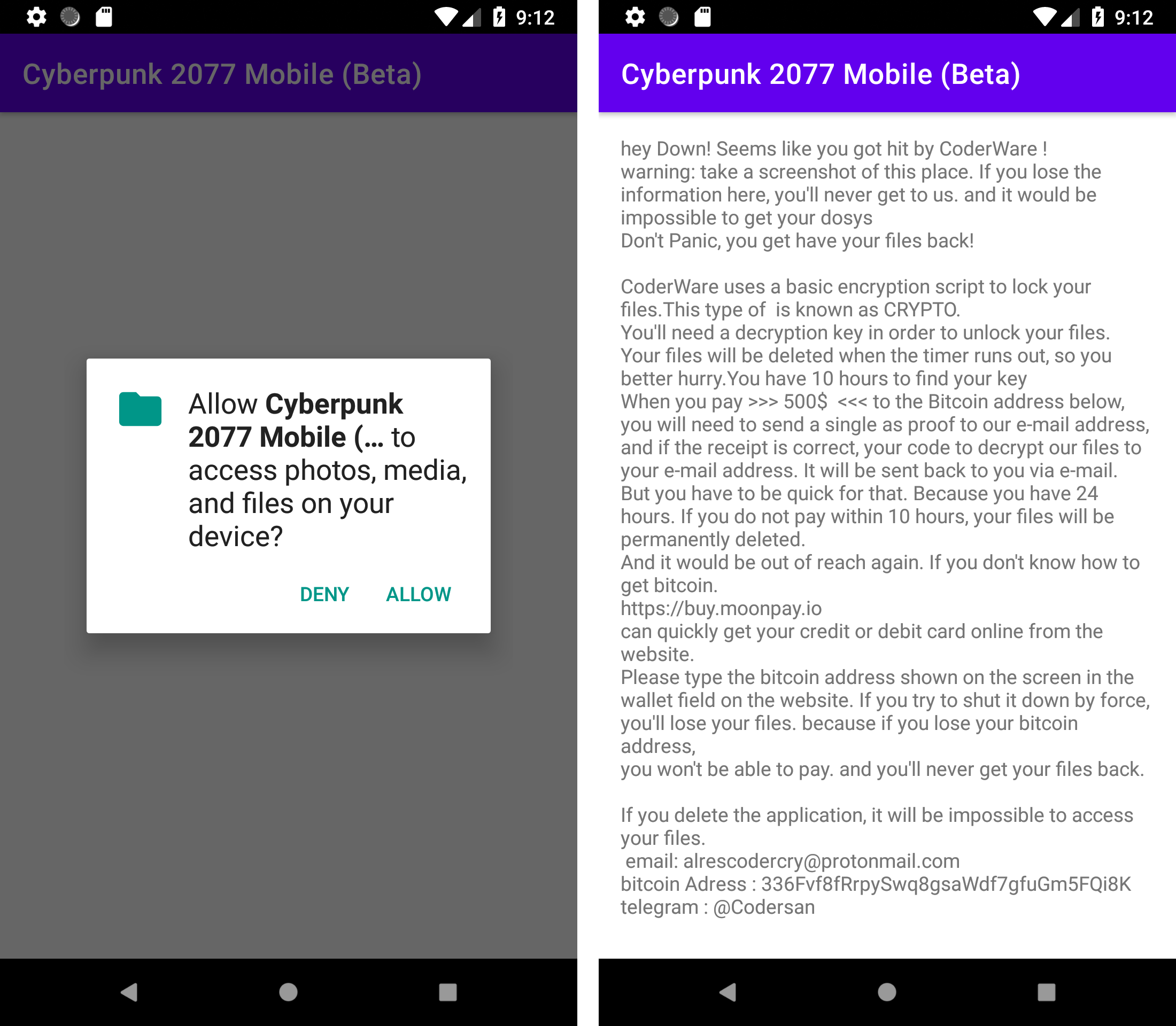
Moving along, on its initial run, the fake beta requests access to files on the device. In theory, an app might need some file access to save or open something, but no game needs your photos and videos just to load. Nevertheless, this app will not run without the permission.
If a user grants that permission, however, they will see a ransom demand, not the game they wanted.
The message is in rather garbled English, and it informs the victim that all of their selfies and other important files are now encrypted. To recover them, the cybercriminals demand $500 in bitcoin within 24 hours. (Or 10 hours. The ransom note mentions both periods.) Anyway, the note continues, if the victim doesn’t deliver the money in time, the malware will permanently erase everything.
According to the note, any attempt to remove the ransomware will be futile and result in the loss of the files.
Are the encrypted files recoverable?
We checked to see what really happens to the files on an infected device. The files are indeed encrypted and assigned the extension .coderCrypt. In addition, the malware places a README.txt file, containing the same ransom message, in each folder.
However, the files are recoverable. That’s because the malware uses the RC4 symmetric encryption algorithm. The symmetric part means the same key both encrypts and decrypts the files. In this case, the key was hard-coded into the app, and in all of the samples that we encountered, it was this: 21983453453435435738912738921.
Because RC4 is quite common, it is possible to recover the files for yourself, for example, by using an online RC4 decryption service or contacting our user support team. What’s more, at least for the version of the malware we examined, the 10- (or 24-) hour deadline is completely irrelevant. The ransomware won’t delete anything after a time — its code contains no such function.
That said, saving a copy of the encrypted files before attempting to restore them is worth your time, just in case the recovery utility fails.
Cyberpunk 2077 ransomware: Windows version
Regrettably, files encrypted by ransomware are not always easy to recover. For example, the authors of the fake beta Cyberpunk 2077 for Android are also distributing ransomware for Windows disguised as the same game. In that case, however, the key is not hard-coded into the app, but randomly generated for each infection case, so victims have no easy way to decrypt affected files.
Should you pay up?
At the time of this writing, more than $8,000 in bitcoin had been transferred to the cybercriminals’ wallet. Meanwhile, file recovery is in no way guaranteed. The ransomware creators might simply disappear with the money or, finding victims willing to pay, demand more. Therefore, we strongly advise against paying the ransom.
Kaspersky experts help ransomware victims by studying malicious code and inventing ways to decrypt files — in other words, we write free decryptors. You can find many of them on the NoMoreRansom website, created specially to counter such attacks, or on our support website. If you do get hit by ransomware, make those resources your first port of call. Even if no decryptor exists for your particular problem yet, it is possible, even likely, that one will appear in due course with a corresponding utility.
How to stay safe from ransomware
The best tip, obviously, is to avoid ransomware in the first place — even ransomware temptingly disguised as a popular game. To protect yourself, observing basic digital hygiene may suffice.
- Download apps only from official stores or from the developer’s official website.
- Scan for news of beta versions, releases, and promotions on the developer’s website. If the developer has no information, or the game is not officially out yet, anything else is fake.
- Use a reliable security solution on all devices to catch malware before it can do any harm. For example, our products nail the fake–Cyberpunk 2077 ransomware for Android with the verdict HEUR:Trojan-Ransom.AndroidOS.Agent.bs, and the version for Windows as Trojan-Ransom.Win32.Alien.ao.
- Back up important files so you can recover them promptly in case of damage or loss.
 gamers
gamers