Nearly every organization in the business of tracking advanced persistent threat campaigns is talking about a new and highly sophisticated attack platform called “Regin” (pronounced: reɪ*ɡən – like the former U.S. president). The general consensus is that Regin is the work of a well-funded nation-state, though it’s impossible to point a finger at any particular country.
It would seem that a number of individuals and organizations had been keeping dossiers on Regin, because as soon as Symantec issued their first version of the report over the weekend, other reports began filtering out, adding to their initial findings. More than one company and more than one researcher (Kaspersky Lab’s Global Research and Analysis Team included) have called this the most sophisticated attack campaign ever analysed.
Highly-complex malware has secretly spied on computers for years, say researchers http://t.co/ip7hkaDBEg pic.twitter.com/TnHhxZS0C4
— The Verge (@verge) November 23, 2014
According to Kaspersky Lab’s findings, the Regin APT campaign targets telecom operators, government institutions, multi-national political bodies, financial and research institutions and individuals involved in advanced mathematics and cryptography. The attackers seem primarily interested in gathering intelligence and facilitating other types of attacks. While much of the intelligence gathered includes spying on emails and documents, the attack group is also relentlessly targeting telecommunication companies, which is normal, and also at least one GSM provider, which is not so normal.
GSM stands for Global System for Mobile Communications. It’s a standard for cellular communications between mobile phones. The best way to think of GSM is as the second generation (2G) of mobile communication technologies. The predecessor to 3G and 4G networks. However, according to reports GSM is the the default standard for mobile networks used by the majority of telecoms. It’s available in more than 219 countries and territories and demands a 90 percent share of the mobile telecom market.
They could have had access to information about which calls are processed by a particular cell, redirect these calls to other cells, activate neighbour cells and perform other offensive activities
“The ability of this group to penetrate and monitor GSM networks is perhaps the most unusual and interesting aspect of these operations,” Kaspersky Lab’s global research and analysis team reported yesterday. “In today’s world, we have become too dependent on mobile phone networks which rely on ancient communication protocols with little or no security available for the end user. Although all GSM networks have mechanisms embedded which allow entities such as law enforcement to track suspects, there are other parties which can gain this ability and further abuse them to launch other types of attacks against mobile users.”
The attackers were able to steal credentials from an internal GSM Base Station Controller belonging to a large telecom operator that gave them access to GSM cells in that particular network, Kaspersky Lab said. My Threatpost colleague Mike Mimoso noted that Base Station Controllers manage calls as they move along a mobile network, allocating resources and mobile data transfers.
“This means that they could have had access to information about which calls are processed by a particular cell, redirect these calls to other cells, activate neighbour cells and perform other offensive activities,” Kaspersky Lab researchers wrote. “At the present time, the attackers behind Regin are the only ones known to have been capable of doing such operations.”
In other words, the Regin actors can not only passively monitor cellular communications metadata, but they can also actively reroute cellular calls from one number to another.
#Regin #APT targets usual victims plus a famed cryptographer and the GSM standard, according to @Kaspersky
Tweet
Another bizarre and curious aspect of the Regin attack group is the story of a famed Belgian cryptographer and mathematician named Jean-Jacques Quisquater. In February of this year, reports began emerging that Quisquater’s personal computer had been hacked six months prior. While it isn’t unusual for prominent academics to be targeted in cyber-attacks, the case of Quisquater was slightly different because of similarities between the attack that targeted his machine and a separate attack targeting the Belgian telecom Belgacom.
The latter incident was the subject of an Edward Snowden revelation claiming that the attack had been orchestrated by the NSA and its British counterpart, GCHQ. Of course, many media outlets have alleged that these similarities suggest that U.S. and British intelligence were behind both attacks. While neither the Kaspersky Daily nor Kaspersky Lab will cosign those allegations, it was reported by a number of news outlets at the time and does bear mentioning.
In addition to the story of Quisquater and the fact that it targets GSMs, the Regin attack platform also boasts incredible technical sophistication, particularly in its pervasiveness. The attackers established backdoors with their command infrastructure to ensure inconspicuous persistence on the networks of their victims. All of the campaign’s communication traffic was encrypted to make sure attacks weren’t observed, both between the attackers and their control servers and between the victim machines and attack infrastructure.
Most of Regin’s communications occur between infected machines – dubbed communication drones – on the victim’s network. The reason for this is twofold: it allows for deep access while also limiting the amount of data exiting the network en route to a command and control server. When you see data leaving the network and trtravellin to an unknown network, that raises alarms. So this in-network peer-to-peer communication makes it more difficult for network monitors to realize an attack in ongoing.
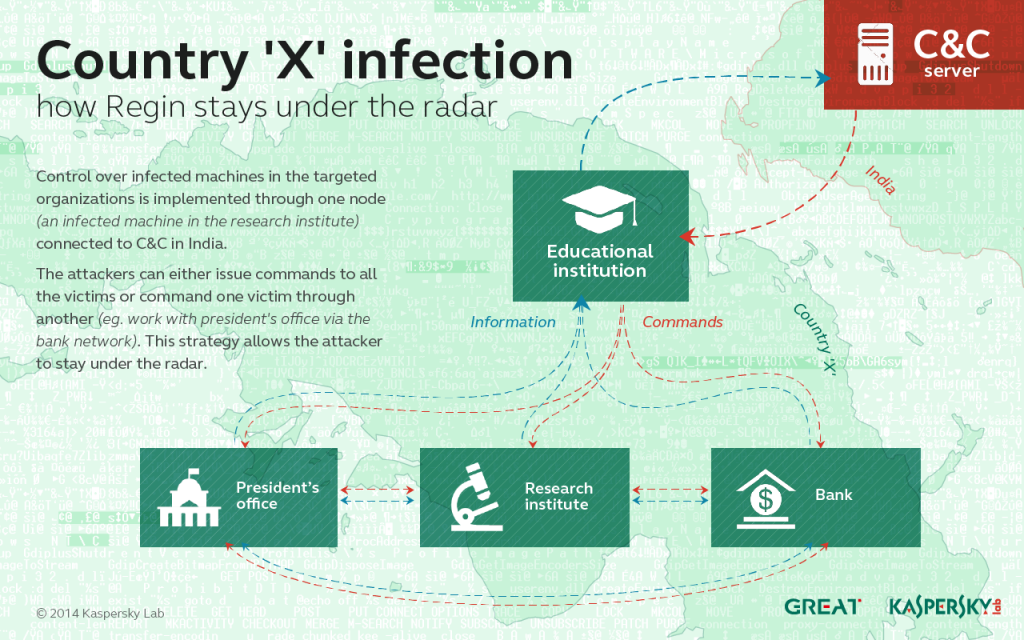
In one unnamed Middle Eastern country, every single victim network identified by Kaspersky lab communicates with all the other networks in a sort of peer-to-peer structure. The network included the president’s office, a research centre, an educational institution network and a bank. One of the victims contains a translation drone that is able to forward the stolen data packets outside of the country, to the command and control server located in India.
“This represents a rather interesting command-and-control mechanism, which is guaranteed to raise very little suspicion” researchers wrote. “For instance, if all commands to the president’s office are sent through the bank’s network, then all the malicious traffic visible for the president’s office sys-admins will be only with the bank, in the same country.”
Absolutely #1 coverage of #Regin #malware espionage campaign, must read to get the whole picture: http://t.co/M1pEhnxCRa by @KimZetter
— Eugene Kaspersky (@e_kaspersky) November 24, 2014
Regin is deployed in five stages giving the attackers deep access to a victimized network with each stage loading subsequent parts of the attack. Modules in the first stage contain the only executable stored on the victim’s computer, and they’re all signed with phony Microsoft and Broadcom digital certificates in order to seem legitimate.
Kaspersky products detect modules from the Regin platform as: Trojan.Win32.Regin.gen and Rootkit.Win32.Regin. Kaspersky Lab has also released a full-length technical paper if you wish to investigate further.
 apt
apt