The story of Naoki Hiroshima and his single letter twitter handle underscores the importance of taking a holistic approach to Internet security and reiterates the reality that the security of one Web account may be intrinsically bound to others in unforeseen ways.
Hiroshima had a monoliteral twitter handle: @N. Apparently he had been offered staggering sums of money from individuals seeking to purchase this handle. I can’t verify this personally, but he claims he had been offered $50,000 to sell access to the profile. He also claims he had been targeted by a never-ending array of account takeover attempts. He regularly received password reset instruction emails that had been initiated by individuals other then himself.
If you’d like to read his story in full, you can find it here on the Next Web. I am not going re-write the story other than to say that a hacker allegedly managed to hijack Hiroshima’s email account and GoDaddy Web domains by authenticating himself with the last four digits of Hiroshima’s credit card number, which the hacker claims he obtained by socially engineering a PayPal customer service representative. The story bears a striking resemblance to the tribulations of Matt Honan (twitter handle: @mat), who in one hour, according to a 2012 Wired article, had his entire digital life compromised. Honan had daisy-chained his Web-accounts together, and an attacker merely compromised one of those accounts before causing all the other dominos to fall.
Let me begin by admitting that it is impossible for me to sit here and tell whoever is reading this the perfect way to secure all of their things on the Internet. Everyone has a different set of needs and a different set of accounts and profiles to meet those needs. The best I can do is examine the widely used services and attempt to establish a set of broad rules to follow that will hopefully keep users form being socially engineered in this way.
Consider this posting a broad overview that aims to take a holistic approach to security by securing all your accounts. Starting this month, we will expand on this by publishing tutorials examining how to secure specific Web accounts. You can get an idea of what these will look like by checking out this Twitter security tutorial.
First things first: run some sort of strong antivirus product so you have protection against malicious key-logging software, trojans, and other threats and malware. Second – as always – install your updates. Without these basic precautions, all other measures are essentially useless.
Some other broad notes before we go to specifics: you need to have different passwords for all your services. If it is too hard to remember, you can use a password manager that will remember your passwords for you.
You really want to set up a dedicated email account for the sole purpose of recovering passwords for your other accounts. It’s recommended that this is a separate account whose only purpose is to backup your other Web accounts. Ideally this is a secret mail account that only you know about. It’s also a good idea to maybe have more than one recovery account so that you aren’t keeping all of your eggs in one basket. However, we understand if you don’t want 1000 email accounts. Microsoft or Yahoo have alias features that may be useful to users that are wary expanding their digital footprint. For example, if you are joebloggs@outlook.com, you could make an alias account with something along the lines of can [secret address]@outlook.com, which will lead to the same mailbox.
Let me be clear, this recovery email is key. If someone gains control of the account through which you can reset all your other accounts, then you are finished. At that point, all of your accounts are compromised.
We begin with Google. The first thing you should do is back up your Google account with that recovery email address we were just talking about. This way, if your account is hijacked, you can send a password reset to your recovery email address and regain access to your account. You should also link the account with your mobile device, so that you can enable two-factor authentication, which we will get to in a moment.
Your Google account has a permissions section, where you can look at all the apps and services that have access to your Google account. Make sure everything in there is legit periodically. If you happen to notice something you don’t recognise, then you should research it. If you still can’t figure out what it is or it turns out sketchy, revoke its access to your account. It’s probably a legitimate application, but it could be malicious and could potentially and theoretically be providing an attacker access to your Google profile.
Again, the reason we wanted to link your account with a mobile device is so we can set up two-factor authentication. This way, you’ll have to approve every account log-in from a new device with a 6-digit code sent via SMS to your mobile device. I admit, two-factor is a bit annoying, but it represents a massive barrier for entry. Now if an attacker wants in to your account, he’ll either have to steal your phone or hack Google, which is probably possible, but I haven’t seen or heard of it being done… yet. You can also set up app-specific passwords if you access gmail on your iPhone or other mobile device – where SMS-based two-factor is not available. This is definitely inconvenient, but probably a good idea as well. We will get into it in one of our video tutorials at a later time.
Beyond two-factor, you should set up mobile alerts so that you get a text message any time anyone tries to change your password or access your account form a strange location. Other than these, just keep an eye on the ‘Recent Activity’ log to make sure everything in there is legitimate. If you see something strange, and by strange, I mean activity initiated by someone that isn’t you, then it is probably time to change up your password. Android devices and Google Wallet – each accessible through your Google account – hold highly sensitive information like credit card data, so you want to make sure that is all locked down.
It’s worth looking into payment-specific security measures with your card providers, online banking accounts, or within Google’s specific services as well. Also, many folks are using Google in combination with their own domain. It’s worth reiterating that an attacker may try to hijack your domain and use that as a ransom to access your other account (as was the case for @N) or even leverage that access to hijack your other accounts (as was the case with @mat).
Apple
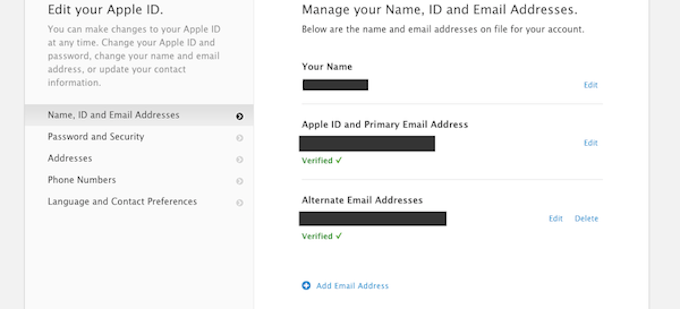
You’re going to want to do some similar things with your Apple ID (if you have one). In order to access that, you can visit appleid.apple.com. Again, you’ll want to set up two-factor authentication. This way you will get an access code on your mobile device every time you attempt to make a change to your Apple ID account. This is good for two reasons. One is that it represents a second barrier of entry other than your password. The other is that if you get a two-factor SMS when you aren’t accessing your Apple ID (or expecting one), then there is a good chance that someone other than you is trying to access your Apple ID. Other than these, you’ll probably already have set up security questions. Make sure they are not easy to answer. I don’t like pre-set security questions, but when I have to use them, I try to choose subjective questions that an attacker could not find the answers to on the Internet. I also recommend setting up a rescue email address just in case things get really dire. The email you have already linked to your Apple account should act as your primary rescue email, but it cant hurt to have a second rescue email. It probably goes without saying, but you want to make sure the password to access your Apple ID is strong as well and different from your email and other passwords.
NB: some services – as the @N story indicates – accept the last four digits of an associated credit card as sufficient proof of account ownership. Apple is not one of those services, but for services that do accept this, it is probably a good idea to dedicate a specific payment card for those accounts. In this way, if an attacker figures out the last four digits of your credit card, that attacker will only compromised that one service, rather than every service that accepts this method of proof-of-ownership.
PayPal
There are two schools of thought here. On the one hand, a PayPal account opens up a new avenue of access into your online banking account. On the other hand, PayPal is an effective way to limit the exposure of your online banking information to third party vendors. For example: if you buy something from a small retail site, there is no real way of knowing what is going on in their backend or with their payment processor. In these cases, no one can really guarantee that they aren’t storing sensitive information like your CVV in plain, unencrypted text. Because of this, it may well be a great idea to use PayPal for online transactions in which you aren’t comfortable handing your payment information directly to the merchant.
Furthermore, to PayPal’s immense credit, the service they provide is incredibly convenient as well as widely used by consumers and accepted among online merchants. Their attitude – like many service providers – is sort of a “trust us” one as far as security goes, but they do offer a few strong protections. The first is a withdrawal limit, which is good (unless your account gets hacked, in which case an attacker could easily increase that limit). I definitely recommend setting a withdrawal limit.
The second – more important – security feature offered by PayPal is there “Security Key” setting. They don’t call it such, but the feature is tantamount to two-factor authentication. They offer users a couple of options. One, which is free, is standard SMS-based two-factor. You give PayPal your mobile number, agree to terms, and they send you a one-time access code whenever you try to sign in. Again, this is strong security, and because it raises the barrier for entry and it potentially alerts you if someone has stolen your password and is trying to log into your account. You can also pay $30, and PayPal will send you a credit card-sized key creator. You press a button on your key-card and it generates a one-time access code – similar to secure ID cards.
They also offer the option to change the validation mechanism for customer service phone calls. By default, it’s a credit card number, but there’s an option to set up a special numeric code for the purpose. It’s smart for the reasons we discussed above.
Beyond this, as always make sure your password is strong and make sure your account has a mobile device attached to it so PayPal can send you alerts about password changes and suspicious account activity.
You can find an extensive overview of useful security and privacy features for Twitter over at Threatpost. In general though you’ll want to set a strong password and use the service’s two-factor authentication feature for all the reasons mentioned repeatedly above. Twitter’s calls it’s two-factor feature ‘login verifications’.
You should also enable the feature that requires you to enter personal information before you perform a password reset. Other than that, you should set up email or SMS notifications for mentions and direct messages, because if someone hacks your account and starts firing off spammy or malware-laden tweets, your friends and followers will probably message you about it. This is something you’ll likely want to know about quickly so that you can resolve the issue as soon as possible.
You should also always keep an eye on the applications linked to your account to make sure they are all on the up-and-up. Furthermore, if there are apps in there that you no longer use, you should go ahead and revoke their access. Unused apps are simply other ways for a hacker to compromise your twitter account.
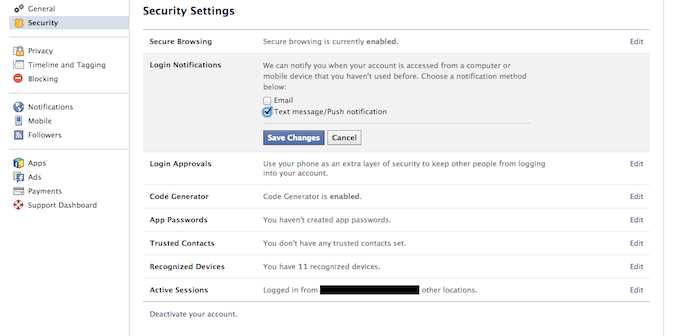
The same idea applies for Facebook. First and foremost – because you have the choice – you’ll want to enable secure browsing if it isn’t already. Set-up login notifications to let you know when there is an access attempt from an unrecognised browser. Set up login approvals, which is the Facebook variety of two-factor authentication. This will make it so Facebook sends a code to your mobile device if someone tries to login from an unrecognised browser. Another thing to consider is the code generator, which is just another way to handle two-factor login attempts. Instead of receiving an SMS code, you log into the Facebook app on your mobile device and it generates an access code for you. Like Google, you can also set up app-specific passwords for applications. Unlike Google, Facebook has a feature that lets you establish trusted friends. This is just another way of recovering your account in case of an emergency. In this case the emergency would be one in which you have no access to the email account through which you would otherwise be able to reset your password in the event of a hijack. Finally, as before, keep an eye on your active sessions to make sure you initiated all of them and – on a related note – make sure that all the devices listed in the ‘trusted devices’ section are in fact devices that you trust.
Amazon
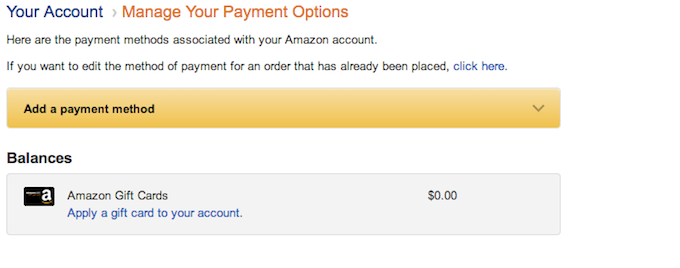
We’re using Amazon here as a sort of proxy for Web retailers. Our first piece of advice – with any online retailer – is to avoid storing your credit card with them if at all possible. Some retailers don’t give you that option; once you enter in your credit or debit card, they are going to store it. Others kindly ask if you’d like to store the card information or use the information just once. There more retailers yet that will store you card date, but – like Amazon – allow you to manage it. In these cases you can save your card data in their servers, but go back and delete it later.
Beyond this, as far as I know, Amazon’s Web-hosting services offer two-factor, but their shopping service does not. So, make sure your password is strong and make sure you have your account backed up with a securely configured email address and link the account to your mobile device.
Like Facebook, you’ll want to head over to the manage account settings page and enable secure connections so that you’re always browsing via HTTPS when you are on LinkedIn. You will be able to set up two-factor authentication there as well. Beyond these, and generally speaking: we want to limit the amount of personal information we post in public places. Especially in a place like LinkedIn where personal information likely includes potentially sensitive information about where you work and what you do for a living. The more information we post, the more likely it is that an attacker can impersonate us and convince humans or machines to grant them access to accounts in which they do not belong. In addition to this, the more work-related information we post, the easier it is for hackers to phish the people we work with.
Yahoo
Yahoo just recently implemented HTTPS, which is nice. It also has a two-factor authentication option, which we recommend using. And don’t forget to set up an emergency recovery email address. Yahoo is another service that requires security questions. Again, whatever the answers to these questions are, make sure they aren’t easily found out online or otherwise.
Yahoo also offers an interesting anti-phishing protection that presents users with a special seal when they sign into a legitimate Yahoo web property. This way, if someone hits you with a phishing link, and redirects you to a page purporting to be a Yahoo log in page, you’ll know, because there will be no security seal.
We’ll dig deeper into the security and privacy settings with a video at a later time.
Microsoft
Another Microsoft service worth keeping an eye on is Xbox Live, especially considering the increased connectedness of Microsoft’s newest console offering, the Xbox One. I haven’t had a chance to really poke around in the new console, but I’ve been on Xbox live on the 360 for years. If you log into your Xbox Live web account you will be given the option of establishing two-factor authentication, setting up a back-up email address, and choosing if and when you want to receive security notifications. These are all important measures to help secure your Xbox Live account, but these are also helpful because your Live account likely contains a credit card. The last four digits of that credit card, which – again – can be used as proof-of-ownership for other accounts, are accessible and viewable within your Web account.
–
This is all for now, but check back soon for our video-tutorial series in which we’ll likely examine the security and privacy settings you should know about for all these services and more.
 data protection
data protection




 Tips
Tips