Hardly are there any folks around who do not use Internet messaging. Just WhatsApp alone is installed on hundreds of millions of devices worldwide and processes a total of tens of billions of messages daily. Don’t forget about Skype, Viber, ICQ, and about a dozen other less popular messengers, including built-in messaging capabilities in Facebook, LinkedIn, and alike. However, with instant messaging services enjoying such popularity, an issue of privacy of message exchange comes to light. This extra cautiousness may seem absurd, provided how much information we readily share on the Internet daily, but there are cases when the correspondence has to be totally, entirely private without any possibility of any third party breaching in. Can we communicate online in such a manner that nobody would smell a Snowden? Let’s have a look.
Prologue
To approach this issue with a shorter pole, we must consider the ways a message chain or voice communication can get exposed to a third party. The options are not that many. Any message of whatever nature, including text, video, photo, or voice, is, firstly, recorded on local storage volumes on the sender’s and recipient’s systems; secondly, transferred via wired or wireless networks; and, thirdly, is processed by the service’s server (well, not obligatory). And if one can, to some extent, control the access to the messaging history in the first case, the rest of the path the message travels is completely out of control. Surely, encryption can save the day, but it is not completely fool-proof: who can guarantee that the protocol, especially if it uses a common encryption algorithm, is positively vulnerability-free?
Take Skype, for instance. A while ago, it was considered to be, besides a pretty good means of private messaging, an unassailable fortress which would yield to nobody, including single hackers and powerful government organisations. But since Skype Ltd. lost its independence after being acquired by Microsoft, things changed, and now we cannot be sure about Skype messaging being 100 percent secure.
The WhatsApp service processing tens of billions of messages daily can hardly be considered safe. News about vulnerabilities (even if only in the Android version, excluding other platforms) appear at least monthly, adorned with details which make your insides churn. For example, a recent study of the application proved that an encrypted file storing the history of messaging on your device can be hacked in a matter of seconds with a simple script. On a side note, the recent acquisition of WhatsApp by Facebook cannot speak in favour of safe messaging: the fact that Mark Zuckerberg paid billions of dollars for the developer team and technology, and not for the user data, is unheard of.
To do justice to the aforementioned services, other free messaging platforms, from Viber to iMessage, have the same kind of problems. All of them allow for relatively easy ways to get access to private correspondence. So, to some extent, it might even be better if such services are property of large corporations which are entitled to prove their case to government and, more critically, to law enforcement authorities. Fortunately, for any action there’s a counter-action: with so many unsecure messengers around, a number of presumably safer solutions sprang to life. Are they capable of saving the vital problem of privacy? Let’s find out. But first, you have to decide which level of security would suit you best.
There is a funny term – ‘theatre of security’. It is quite self-explanatory and means ostensible security measures which are used to provide an illusion of action without considering efficiency of the effort. If we were to draw analogies, we might remember anti-terrorist security measures on public transit facilities: the suspicious objects and individuals are checked on selected stations only. House intercom deployed in numerous residential buildings can also serve an example of this ‘theatrical security’. The same characteristics can be applied to the software sphere, especially in the case of instant messaging. That does not necessarily mean that some instant messengers are completely useless: it might well be that they could make a nice alternative to users who are not fussy about the privacy or high level of security. The guards taking care of anti-terror inspection on the underground have been able to offer some level of protection, after all. So, having said that, we must acknowledge you can still use a once-failed messaging app, provided they know what they want to be protected against: from a jealous partner eager to read their private messages, or people who are keen on hijacking the traffic on its way from a sender to a recipient. And yes, we do not consider situations when the person breaching your privacy is in fact your interlocutor: in this case, no advanced software would ever be able to protect you. So, if you don’t have trust in your vis-à-vis, just don’t message them!
Let’s have a look at popular options offered in two categories.
The illusion of safety
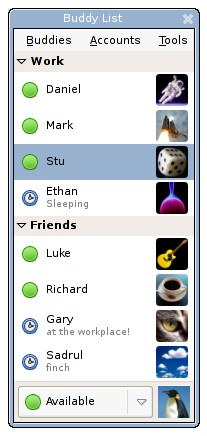
We categorised messengers not performing to the expected level of security or not guaranteeing protection from correspondence hijacking on the way (man-in-the-middle attack) into this list.
In a sense, it is a unique messenger: all messages coming via Confide are depicted as rectangular boxes hiding the text which becomes visible only upon swiping it. Moreover, the application does not offer long-term storage for history of messaging, so even if the culprit gets the phone, he would not be able to discover your correspondence. On an attempt to make a screenshot of the message, the user will be pushed back to the contact list and his interlocutor will get a respective notification. These capabilities are extensively highlighted by the app developers: you may read but you may not save. But there’s one thing. Should a user want to record the message, he might not be obliged to make a screenshot and instead use a camera to register the communication process word-by-word. In this case, the application can be categorised as a program which exercises ‘theatrical security’: a state-of-the-art protection of messaging and screenshot disablement just to provide an illusion of safety. So it might suit those who want to play at being secret service agents.
Not that elegant in terms of design, yet ambitious, this application positions itself as a solution leaving no trace of correspondence on the device: it erases (in some cases, irrevocably) message history both from the device memory and the server, protects the messages with government-grade security algorithms, provides means of controlling the duration of storing period for the recipient, and disables the message copying. The latter, similarly to the previous application, leans on the technical limitations of the smartphone functionality – the approach which is useless before a camera integrated in practically any device on Earth.
When talking about the safe instant messengers, how can we ignore Telegram, which is presumably the most publicised messenger with a ‘secure’ tagline. How come it is included in our ‘theatrical security’ messenger list? Well, take the fact that ‘unprecedented’ security of messaging vouched by the developers of the app was never objectively proven, although used to be a subject of fair criticism.
Many would remind us of a $200,000 bounty for hacking Telegram’s MTProto protocol announced by the creators of the solution. In fact, for many, this aplomb might be a powerful argument for the messenger’s reliability. However, we must draw your attention to the fact that this contest, presupposing an attempt to decipher a message transferred to a recipient from a sender, strongly reminds us of an attempt to test the endurance of the tank protection skin by a pistol when in fact it must effectively be done with help of an anti-tank weapon. In other words, the means and tools of hacking this messenger are initially inefficient and unable to stress-test the protocol. Pointing out this fact, a cryptofails.com author also noted that MTProto is a highly insecure and unreliable algorithm ‘which ignores all meaningful cryptography studies published in the last 20 years’, and suggested the developers contract a real cryptography expert to audit Telegram.
One more curious detail: regardless of a complex protocol serving the basis for Telegram, it is vulnerable to the straightforward app attack. Yes, we are not talking about the traffic hijacking but about a way simpler thing. The thing is that, on registration, a user receives a text message on the phone and has to enter the received security code to activate the app. But if a hacker gets hold of the victim’s text messages, he can activate his copy of the app with another person’s code and, consequently, receive all messages sent to the victim. Considering the fact that the ‘Secure chat’ capability is not enabled by default, the privacy of correspondence is to a high extent compromised.
What is good about Telegram is its speed: the messages are indeed sent and delivered literally instantly, and notably quicker than via other messengers. So, is it a speedy messenger? Yes! Is it safe? Well, just relatively.
Honest safety
This category includes apps and services which provide a level of security fully compliant with officially proclaimed features and are able to substantially protect the access to correspondence from third-party assaults.
This is a Swiss project which enjoyed growing popularity after the announced acquisition of WhatsApp. The developers guarantee the safety of correspondence: firstly, the software reliably encrypts the data in transfer; secondly, it protects user privacy via the face-to-face confirmation when a new contact is added. The latter presupposes that the corresponding users have to meet in person and scan QR codes from each other’s phones, which looks sensible from a security standpoint but practically complicated in many cases. Of course, you can add a new contact in an old-school manner by manually typing the user ID, but in that case, the level of security is lower. It should be noted that the developers are not overstretching themselves to prove their messenger offers an ‘unprecedented’ level of safety and do not make false promises. And yes, one more thing: the app is worth two dollars, paid once.
This is one of very few projects developed by renowned cryptography gurus. In our case, the dev team includes Phil Zimmerman, the author of PGP encryption technology. Similarly to Telegram, the Silent Circle service relies on a purpose-made algorithm, SCIMP. Its advantage lies in capability of fully erasing sent messages without a trace: neither a sender, nor a recipient would ever be able to recover any part of the correspondence on their devices. This capability is enabled both manually and automatically: within a certain period of time after the messages were sent, they will be deleted on their own accord. But the main merit of the messenger is that the software applies powerful encryption to the traffic, so it is rendered simply useless to hijack. By the way, the solution presupposes to transfer encrypted traffic including, besides text, video and audio messages. As for the rest, the messenger is, unfortunately, packed with flaws. They start with the ambiguous registration process and end with the price: one-year subscription for Silent Circle is worth 100 US dollars.
A free TextSecure app was warmly credited by the audience, and the developer, WhisperSystems, was highly spoken of by Edward Snowden. The software is effectively a very simple messenger, without any bells and whistles or complex settings, providing powerful encryption for both outbound and locally stored messages. To name a couple of small drawbacks: the app cannot be praised for rich functionality and also features Android-only compatibility, which is a serious imperfection but developers say there will be iOS version very soon. On a side note, one of its founders is Moxie Marlinspike, a famous encryption specialist.
$50 – this is the price for, probably, the most expensive, yet the most reliable, iOS-compatible messenger – SJ. Its main advantage lies within the ability to use individually picked complementary keys when sending a message. Or it can be rendered the main disadvantage, depending on the user’s technical literacy. To those who got used to regular Skypes and WhatsApps, SJ may seem extremely difficult to use, so it is all about the choice: whether an unprecedented level of security or ease of use.
This is a popular open-standard messenger with a complete set of security protocols. It is free and compatible with Windows, Linux and Mac systems – however, the developers recommend Apple users take advantage of Adium, which supports encryption protocols up to an impressive 4096 bit which is a bit more than enough. The software seamlessly supports the OTR (Off-the-Record Messaging) protocol serving to ensure the privacy of correspondence and also has a lot of different plug-ins. A significant advantage of the solution, especially considering the topic of the article, is the support for XMPP/Jabber, a decentralised, flexible, and safe instant messaging system.
Similar to other solutions listed in our material, Cryptocat is a messenger with message encryption capability; yet, unlike others, it functions as a desktop browser plug-in for Chrome, Firefox, Safari, and Opera. For Mac OS X and iPhone users, however, it is available as a separate app. Some time ago, the service underwent a successful attempt to compromise in- and outbound data, and the developer team put in an immense effort to increase the level of safety. The notable fact is that Cryptocat is constantly updated: the latest version was available in early April. Funny, that the project creator posted the following text on the project website: ‘Cryptocat is not a magic bullet. Even though Cryptocat provides useful encryption, you should never trust any piece of software with your life, and Cryptocat is no exception.’
Coming soon
We’ve listed some solutions under this heading since their creators have not yet fully launched the product, but have disclosed certain characteristics. Let’s see how much these services would live up to the expectations set by their developers.
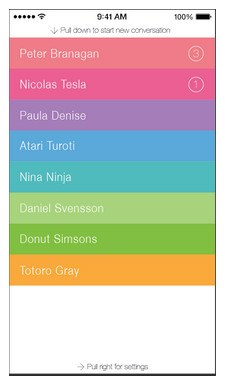
Regardless of the fact that the Heml.is service is still under development, it’s attracted a good deal of attention. It comes as no surprise, as one of the project participants is none other than Peter Sunde, one of the founding fathers of The Pirate Bay torrent tracker. Among the service features are an XMPP-based protocol and PGO library as an encryption basis. Among immediate advantages, we can enumerate a pleasant design (judging by the available presentations) and cross-platform compatibility.
Bottomline: a promising safe messenger; not available, though.
Tor Instant Messaging Bundle (TIMB)
The news of the Tor dev team working on a messenger dates back to end of February. Initially, the product was supposed to be based on the aforementioned Pidgin app, but later on, the choice was made in favour of Instantbird. TIMB, as a notion, will also support the OTR protocol we talked of earlier, and the dev team would comprise of independent security experts as well. The app distribution approach is likely to be exercised as a part of the Tor Launcher bundle, but the information on the app availability is not disclosed yet. In any case, TIMB is worth waiting for: which other messenger would not only encrypt your correspondence but as well preserve your anonymity?
Epilogue
It is obvious no cryptomessenger is ideal. Anyway, you must compromise on either your budget, ease of use, or the security level. Besides, secure online communication protection is not performed by one certain program – it has to be a combination of security means. Also, no software is able to offer a 100% guarantee of privacy if you do not trust your vis-à-vis and other interlocutors, or if your network is controlled from the outside, or if your device has been infiltrated by a spying malware; namely, a keylogger. Considering the solution for the first problem is not immediate, the rest of them are easily dealt with: a paid VPN access for your system is about $5 a month, yet it might save you from threats coming from public Wi-Fi networks. As for keyloggers and other malware, there are reliable protection suites like ours. With such protection means at hand, just add any XMPP/Jabber-based messenger and rest assured your communication on the Internet is safe.
 encryption
encryption










 Tips
Tips