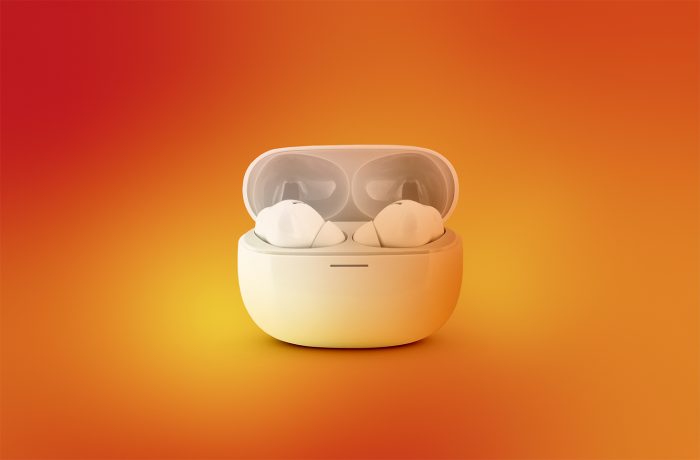
Are your Bluetooth headphones spying on you?
Breaking down the WhisperPair attack, which allows victims to be tracked via ordinary Bluetooth headphones.
8 articles
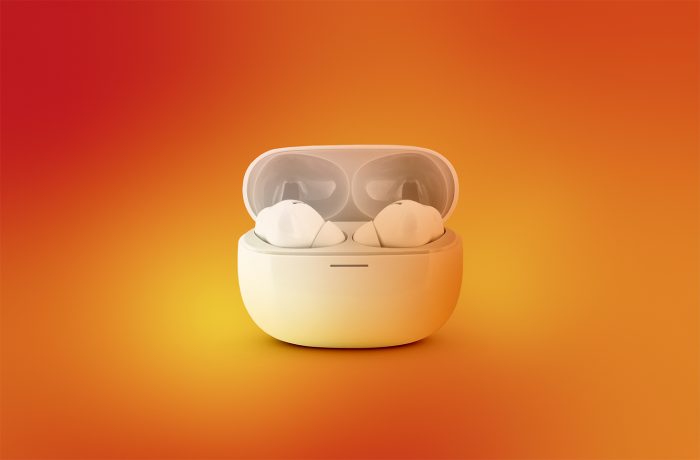
Breaking down the WhisperPair attack, which allows victims to be tracked via ordinary Bluetooth headphones.

How researchers hacked DeckMate 2 card shufflers, and how the mafia exploited those very vulnerabilities to cheat at poker.

Researchers have discovered several potential attack vectors targeting bicycles fitted with Shimano Di2 wireless gear-shifting system.

Small beacons like AirTag make it easy to find a lost wallet or keys — but are also often used for covert tracking. Now you can detect stalkers and protect yourself — regardless of what kind of smartphone you have.

A researcher has discovered a vulnerability in the Bluetooth protocol implementations for Android, macOS, iOS, and Linux, allowing devices to be hacked remotely.
We investigated three cases of ATM robbery — involving remote-controlled malware, a Bluetooth keyboard, and a drill.

Everyone loves the hands-free convenience that Bluetooth enables — some people love it a little too much and insist on wearing their Bluetooth ear pieces every waking hour like they’re