Messaging apps are not only a useful tool for keeping in touch, but also an open window through which intruders are able to climb into our lives. It seems like only yesterday that we were discussing the Android Trojan Skygofree, which spies through Facebook Messenger, Skype, Viber, WhatsApp, and other platforms. Well, today we’re going to talk about a new multi-functional infection detected by our experts. It stalks desktop computers and spreads through Telegram — and in a very ingenious way, too.
Malware becomes a kitten picture!
One of the main tasks of Trojan creators is to persuade users to run malware. To do this, they grab from a bag of tricks to mask dangerous files as innocuous ones.
For this particular trick, keep in mind that some languages are written from right to left — for example, Arabic and Hebrew — and that Unicode, the computing standard and near-ubiquitous set of characters, provides a way to change the direction of written words. Use a special invisible character and the string of letters that follows is automatically displayed in reverse order. That’s what hackers exploited in a recent attack.
Suppose a cybercriminal creates a malicious file called Trojan.js. As you can see from the JS extension, it’s a JavaScript file, and it might contain any executable code. A cautious user immediately smells a rat and does not run it. But the scammer can rename it — for example, like so: cute_kitten*U+202E*gnp.js.
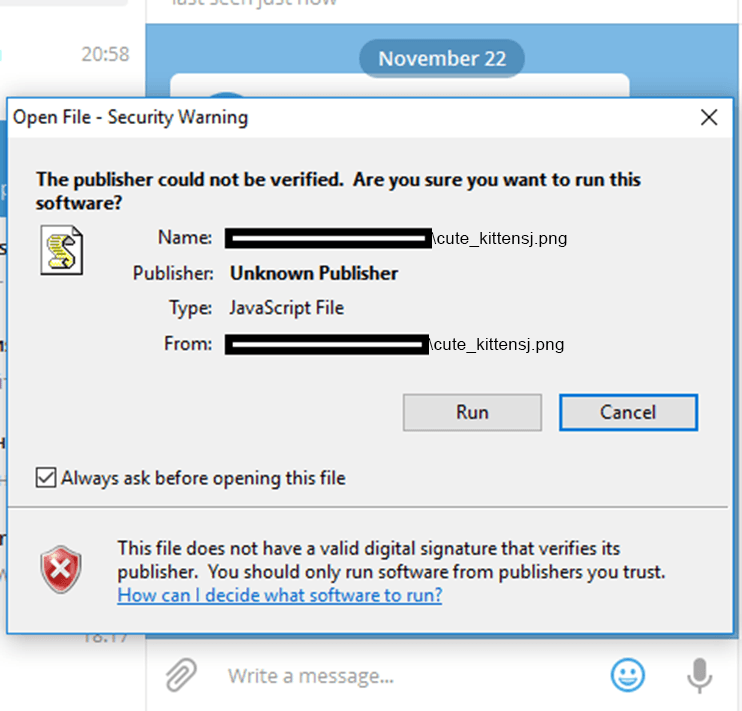
That would look even worse to a user, but here, U+202E is the Unicode character after which letters and punctuation marks are displayed from right to left. The resulting file name will be shown as follows: cute_kittensj.png. Now the file extension seems to be PNG — it looks like a perfectly normal picture file, but it is really a JavaScript Trojan.
The file-renaming trick using Unicode is not new. It was used to mask malicious e-mail attachments and file downloads almost a decade ago, and many environments are already protected against it. But when Telegram was targeted for the first time, it worked. In other words, Telegram has (or rather, had) the so-called RLO vulnerability, which was what our researchers picked up.
Kitten picture turns into a miner or backdoor
The vulnerability was detected only in the Telegram Windows client, not in mobile apps. Our experts discovered not only its existence, but also that attackers were actively using it. Victims’ operating systems should warn them if they are about to run an executable from an unknown source — which ought to set off some alarm bells — but many people click Run without looking at the message.
Once launched, the malware really does show a “cute kitten” to quell any hints of alarm. The Trojan comes with different types of payload to run behind the scenes, depending on its configuration.
Payload type one is a hidden miner. Running it, the computer slows down, overheats, and generally busts a gut trying to mine cryptocurrency for the attackers. Payload type two is a backdoor that allows the cybercriminals to control the computer remotely and do anything they like with it, from removing and installing programs to gathering personal data. This type of infection can remain hidden for a very long time without the user suspecting a thing.
Keep calm and carry on
Our researchers promptly reported the vulnerability to Telegram’s developers, who fixed it (much to the annoyance of cybercriminals wanting to exploit it). However, this certainly doesn’t mean that Telegram and other popular instant messaging apps are free of vulnerabilities. They simply haven’t been reported yet. So, to stay protected against future plagues, brush up on some simple safety rules. These are valid for social media, instant messaging, and any other means of electronic communication:
- Don’t download or open files from risky sources. If someone hitherto unknown sends you a picture, think twice about opening it.
- If you see a system warning about opening a file, consider whether the description matches the file you’re about to open.
- Install a reliable security solution such as Kaspersky Internet Security, which will help catch malware masquerading as an image at the download or installation stage — and protect your computer against other infections, too.
 threats
threats

 Tips
Tips