
Android trojan posing as government services and Starlink apps
We break down the BeatBanker trojan attack, which combines espionage, crypto theft, and mining with inventive ways to dig its heels into a smartphone.
250 articles

We break down the BeatBanker trojan attack, which combines espionage, crypto theft, and mining with inventive ways to dig its heels into a smartphone.

We’re diving into why mental health apps have become a headache for their users, and how to minimize the risks of medical data leaks.

Tired of hallucinations in AI overviews, and have no clue as to why or how Copilot suddenly appeared on your PC? Here’s a guide to switching off those intrusive AI features in popular services.

NFC relay attacks, pre-installed Trojans, and other nasties ruining the Android experience in 2026.

Our Android apps are no longer available on Google Play. We explain how to download, install, and update them by alternative means.
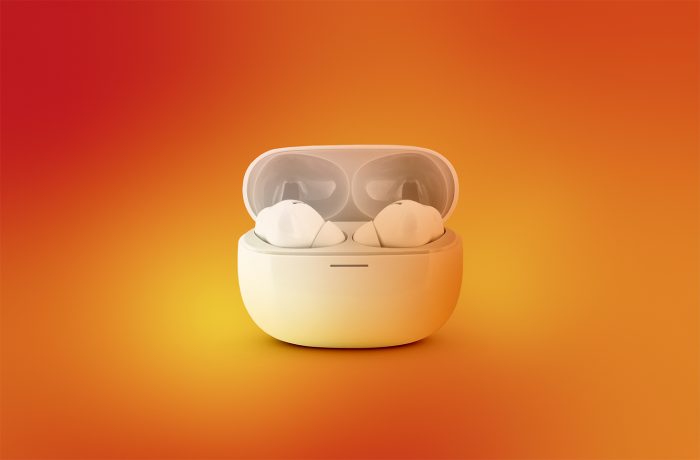
Breaking down the WhisperPair attack, which allows victims to be tracked via ordinary Bluetooth headphones.

How criminals exploit the familiar “tap your phone to pay” feature to steal your money.

Pixnapping is an Android vulnerability discovered by researchers that allows apps to steal passwords, one-time codes, and other confidential information from the screen without any special permissions from the operating system. How does it work, and what can you do to protect yourself?

Which social networks mostly just display your posts to your friends, and which ones use them for AI training and ad targeting? We explore the 2025 privacy rankings for popular social media platforms.

Which messaging apps leak the least amount of your data, and provide the most control over your privacy? Today we discuss the latest rankings of popular communication platforms.

The Kaspersky for Android app can now detect malicious links in notifications from any app.

The internet never forgets — and what kids post or share today can come back to hurt them, either right away or years down the line. Here’s how to shrink your child’s digital footprint without resorting to battles or bans.

How 5G smartphone connectivity can be compromised, and what it means for subscribers.

We explore which messaging apps let you chat without an internet connection or cell service, and why you might need this.


Scammers have figured out how to send text messages that actually bypass cellular networks. How does illicit “SMS blasting” work, why does it matter for travelers, and how to stay safe.

Google has rolled out an update for Android that gives Gemini access to your Phone, Messages, WhatsApp, and Utilities data without your explicit consent. Here’s a detailed guide on how to disable these permissions.

This marks the second time we’ve found a stealer Trojan in the App Store.

Can your photos be viewed, stolen, or deleted when your smartphone is plugged into a public charging station? As it turns out — yes!

Counterfeit smartphones imitating well-known brands and offered online come pre-installed with the powerful Triada Trojan.

A dozen short and simple tips on how to use WhatsApp, Telegram, Signal, iMessage, WeChat, and other messaging apps safely and hassle-free.