From one solution to global protection
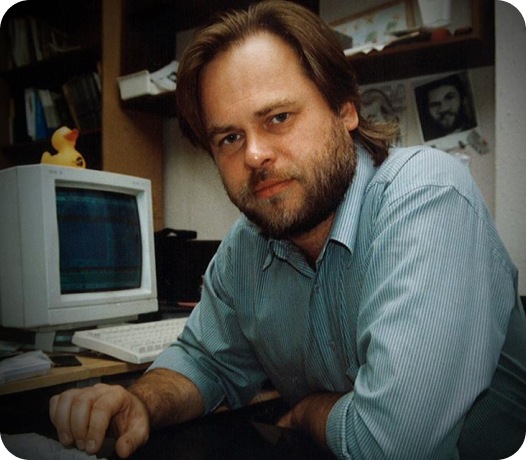
In 1989, Eugene Kaspersky's computer was infected by the Cascade virus. This single moment went on to shape the future of the entire cybersecurity industry.
Starting with the fight against one virus, Eugene then grew Kaspersky into a global leader in cybersecurity, protecting users and organisations around the world from complex and sophisticated cyber threats.