Mobile Security Threats Stay on the Move
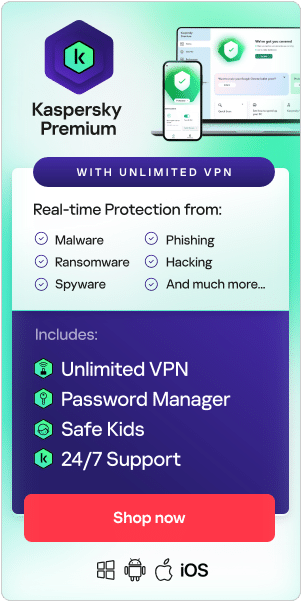
KasperskyAre traditional computers — desktop machines and laptops — more secure than mobile devices such as smartphones and tablets? Even experts do not always agree about this question, because both computers and mobile devices pose security threats. But as long as you take common-sense precautions, you can build solid desktop and mobile security.