The word "hacker" conjures the image of someone with ill intent toward individuals, websites, and company information systems. The prevailing theory is they look for ways to mine company data and destroy or change customer information. Those types of "bad guys" certainly exist — the cybersecurity industry calls them Black Hats, but in reality, they aren't the only hackers lurking in cyberspace.
The Good Guys
Enter the White Hat hacker, the good guy who uses his (or her) capabilities to damage your organization — but only hypothetically. Instead, the real purpose is to uncover security failings in your system in order to help you safeguard your business from the dangerous hackers.
Companies hire White Hats to stress test their information systems. They run deep scans of networks for malware, attempt to hack information systems using methods Black Hats would use, and even try to fool staff into clicking on links that lead to malware infestations.
White Hats are one of the reasons large organizations typically have less downtime and experience fewer issues with their websites. Most hackers know it will be harder to get into systems managed by large companies than those operated by small businesses that probably don't have the resources to examine every possible security leak.
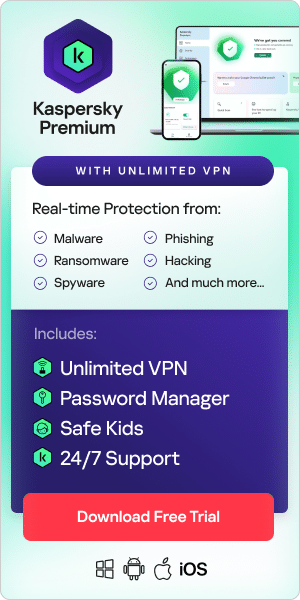
For that reason, it's very important for any online business to make sure it takes strong preventative measures by installing quality anti-malware security, spyware removal tools, and firewall software defense. Customers need to feel secure that online service providers are protecting their data — or they will take their business elsewhere.
The Ugly
Somewhere between white and black lies the ugly — the Gray Hats. Some Gray Hat hackers like to believe they're doing something good for companies by hacking their websites and invading their networks without permission, but company owners rarely appreciate unauthorized forays into their business information infrastructure.
In most cases, a Gray Hat's real intention is to show off his skills and gain publicity — maybe even appreciation — for what he considers a contribution to cybersecurity.
Gray Hats often say they mean no harm with their incursions. Sometimes, they're simply curious about hacking a high-profile system — without regard to privacy and numerous other laws.
Gray Hats assert that the internet isn't safe for business, and they consider it their mission to make it safer for individuals and organizations. They do this by hacking websites and networks and causing chaos to show the world they're right.
In most instances, Gray Hats provide valuable information to companies. Nonetheless, the community of White Hats — and much of the cyber world — doesn't view their methods as ethical.
The More Things Change
It was just a few decades ago in the U.S. that neighbors left the doors to their homes unlocked. Now, doors are rarely unlocked, and most homes have security alarms to protect the property. Owners have come to presume that someone is lurking in the shadows, waiting for them to be careless.
Businesses with websites and information systems are waking up to the same reality as homeowners. They know someone is probably patrolling their internet neighborhood, waiting for the right time to break in and steal customer information.
Additionally, Black Hat hackers may want to plant malware that spies on staff and customer activity.
Although White Hat hackers operate as guns-for-hire, constantly testing a business' information infrastructure to ensure it remains free of threats, it's still essential for companies to employ all the right preventative measures. It starts with installing and maintaining anti-virus software, spyware elimination tools, and strong firewall defenses.
It's not just business operations that are at stake. Clients' information — and their trust in a company's integrity — hang in the balance.
Related articles:
- Computer Viruses and Malware Facts and FAQ
- Most Notorious Black Hat Hackers
- What is Adware?
- What is a Trojan?
- Spam and Phishing